The North Korea-linked risk actor often known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been noticed shifting its ways, leveraging Compiled HTML Assist (CHM) information as vectors to ship malware for harvesting delicate information.
Kimsuky, energetic since not less than 2012, is understood to focus on entities positioned in South Korea in addition to North America, Asia, and Europe.
Based on Rapid7, assault chains have leveraged weaponized Microsoft Workplace paperwork, ISO information, and Home windows shortcut (LNK) information, with the group additionally using CHM information to deploy malware on compromised hosts.
The cybersecurity agency has attributed the exercise to Kimsuky with average confidence, citing comparable tradecraft noticed previously.
“Whereas initially designed for assist documentation, CHM information have additionally been exploited for malicious functions, resembling distributing malware, as a result of they will execute JavaScript when opened,” the corporate stated.
The CHM file is propagated inside an ISO, VHD, ZIP, or RAR file, opening which executes a Visible Fundamental Script (VBScript) to arrange persistence and attain out to a distant server to fetch a next-stage payload accountable for gathering and exfiltrating delicate information.
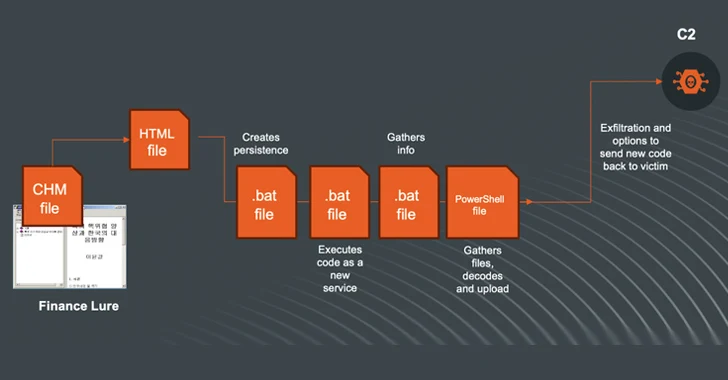
Rapid7 described the assaults as ongoing and evolving, focusing on organizations primarily based in South Korea. It additionally recognized an alternate an infection sequence that employs a CHM file as a place to begin to drop batch information tasked with harvesting the knowledge and a PowerShell script to hook up with the C2 server and switch the information.
“The modus operandi and reusing of code and instruments are exhibiting that the risk actor is actively utilizing and refining/reshaping its strategies and ways to assemble intelligence from victims,” it stated.
The event comes as Broadcom-owned Symantec revealed that the Kimsuky actors are distributing malware impersonating an software from a legit Korean public entity.
“As soon as compromised, the dropper installs an Endoor backdoor malware,” Symantec stated. “This risk allows attackers to gather delicate data from the sufferer or set up extra malware.”
It is price noting that the Golang-based Endoor, alongside Troll Stealer (aka TrollAgent), has been lately deployed in reference to cyber assaults that focus on customers downloading safety applications from a Korean construction-related affiliation’s web site.
The findings additionally arrive amid a probe initiated by the United Nations into 58 suspected cyber assaults carried out by North Korean nation-state actors between 2017 and 2023 that netted $3 billion in unlawful revenues to assist it additional develop its nuclear weapons program.
“The excessive quantity of cyber assaults by hacking teams subordinate to the Reconnaissance Common Bureau reportedly continued,” the report stated. “Developments embrace focusing on protection corporations and provide chains and, more and more, sharing infrastructure and instruments.”
The Reconnaissance Common Bureau (RGB) is North Korea’s main international intelligence service, comprising the risk clusters broadly tracked because the Lazarus Group – and its subordinate components, Andariel and BlueNoroff – and Kimsuky.
“Kimsuky has proven curiosity in utilizing generative synthetic intelligence, together with massive language fashions, probably for coding or writing phishing emails,” the report additional added. “Kimsuky has been noticed utilizing ChatGPT.”